
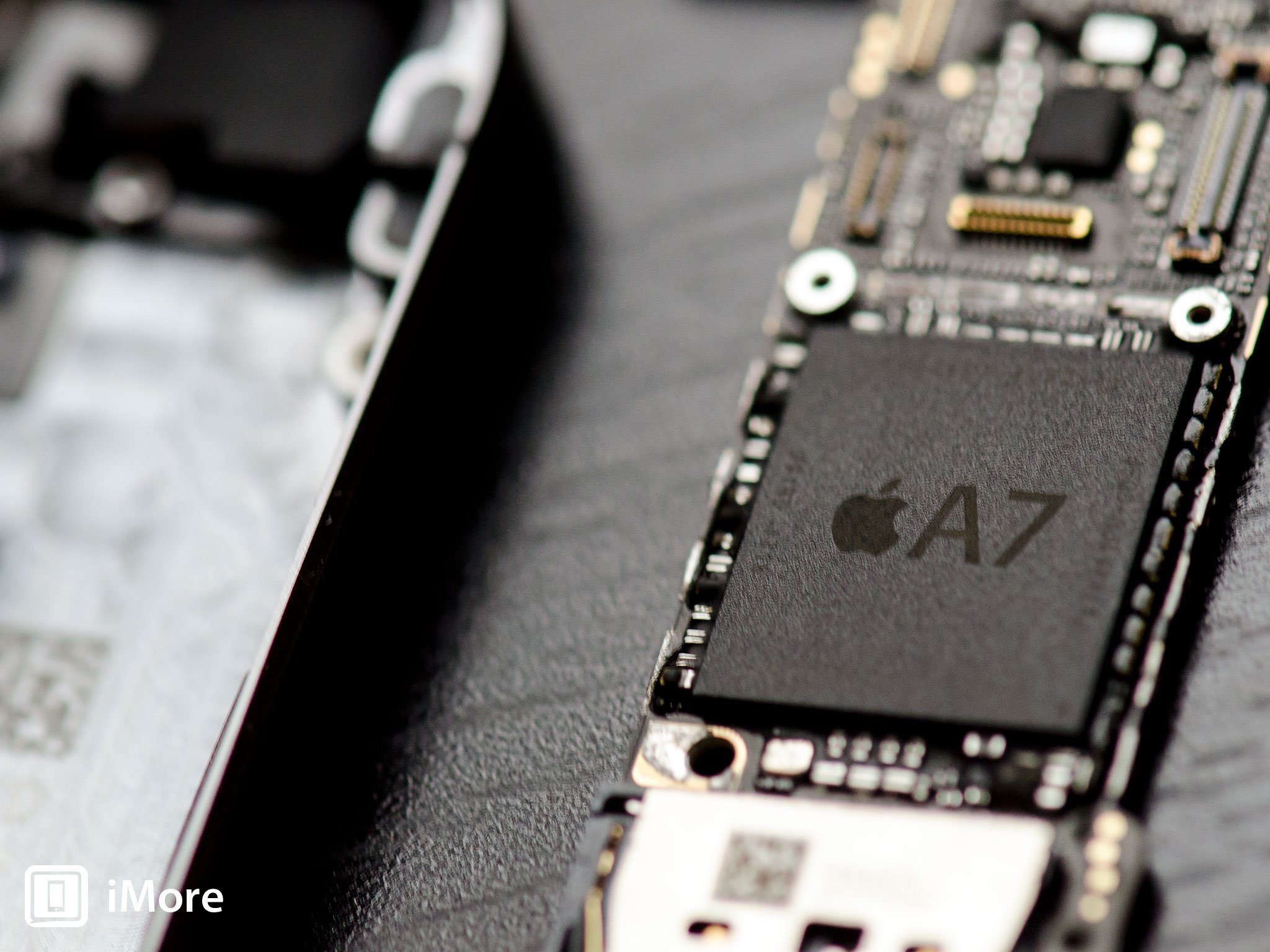
We already know that the iPhone 5s' Touch ID secures your digital fingerprint by storing it on the Secure Enclave portion of the A7 that's only accessible to the sensor itself. But what if that wasn't the only safeguard Apple took in order to protect your prints? We've taken a closer look at Touch ID and through some collaboration with repair company mendmyi, we've found that Apple actually did take extra precautions, but on a hardware level that we've never seen implemented before.
Apple has touted Touch ID to be a secure hardware path since they announced the iPhone 5s. This is Apple's explanation of Secure Enclave on their own website:
Touch ID does not store any images of your fingerprint. It stores only a mathematical representation of your fingerprint. It isn't possible for your actual fingerprint image to be reverse-engineered from this mathematical representation. iPhone 5s also includes a new advanced security architecture called the Secure Enclave within the A7 chip, which was developed to protect passcode and fingerprint data. Fingerprint data is encrypted and protected with a key available only to the Secure Enclave. Fingerprint data is used only by the Secure Enclave to verify that your fingerprint matches the enrolled fingerprint data. The Secure Enclave is walled off from the rest of A7 and as well as the rest of iOS. Therefore, your fingerprint data is never accessed by iOS or other apps, never stored on Apple servers, and never backed up to iCloud or anywhere else. Only Touch ID uses it and it can't be used to match against other fingerprint databases.
Apple has only ever talked about Secure Enclave in regards to protecting our digital fingerprints. They don't make specific mention of any other additional safeguards. However, through some research and testing of our own, we are pretty convinced they didn't stop at just the Secure Enclave.
It seems as though Apple has went through the trouble of pairing every individual Touch ID sensor cable to each individual phone. That's an incredible feat, but also baffling at the same time. But to understand and potentially figure out why, let me explain how we came to this conclusion.
Our investigation into the Touch ID assembly itself started when mendmyi contacted me about an issue with Touch ID on a customer's phone that had been in for their Colour Lab service. The video below demonstrates the issue they were presented with.
In order to try and rectify the issue, many steps were attempted. These included swapping out the Touch ID sensor for one verified to work, replacing the dock connector in which the Touch ID makes contact with, and even replacing the logic board itself. When each different hardware fix was attempted, a DFU restore was performed as well. Nothing worked. All of us were baffled.
It was then discovered that the Touch ID sensor currently in the device was not the original that came in the device. Upon replacing the original, Touch ID once again worked fine.
At this point, we knew there had to be some hardware lockdown going on that we weren't previously aware of. To test this theory, we took two iPhone 5s' that had never been opened before. First, Touch ID was verified to be in working order on both devices. The front assemblies, which contain the Touch ID assembly itself, were then removed from each and swapped into the other. Upon setup, both Touch ID setups failed. When returned to the original device, Touch ID once again operated correctly.
This confirmed for us that the Touch ID component cable assembly itself is tied to each individual A7 chip.
Our next step was obviously to understand why Apple would make this decision. So I asked our resident security expert, Nick Arnott, if he had any thoughts on why Apple would find this necessary. While none of this can be confirmed, these are his thoughts on why Apple may have taken the extra precaution:
It's hard to say why Apple might lock the A7 chip to a specific Touch ID sensor. One possibility could be to try and prevent any sort of sniffing or interception taking place between the Touch ID sensor and the secure enclave. Sort of like a hardware equivalent to SSL certificate pinning. By pairing the A7 chip to a specific Touch ID, this could make it more difficult for tinkerers to try and intercept communications to reverse engineer how the components talk to each other. This could also mitigate possible risks of malicious third-party Touch IDs being installed in a user's device without their knowledge which could capture a user's fingerprint for an attacker, while passing it on to the A7 chip to allow a user to continue to use their device as normal, without any indication it has been tampered with. If Apple instead used some sort of shared key that was used by all Touch ID sensors to authenticate with the A7 chip, it would only take one Touch ID's key being hacked to compromise all of them. Being tied to a unique Touch ID sensor on each phone means installing something like a malicious Touch ID sensor would require cracking each device you want to attack individually.
I think all Nick's points are valid and could certainly explain what Apple was getting at in their own description of Touch ID when they touch on the fact that it isn't possible for your fingerprint to be reverse-engineered. One thing is for sure, I'd be very curious to see if these kinds of security precautions are taken in other fingerprint readers such as the one found in the HTC One Max.
What does all this mean for general consumers, hackers, DIY repairs, and future security standards?

For general consumers, this is good news. It means you've got an extra layer of protection that's specifically unique to your device. A universal hack won't work. For hackers, it means they've got their work cut out for them and if they want to bypass Touch ID, if it's possible at all, it can't be done by modifying the sensor cable itself.
When it comes to DIY repairers, it means your job just got a little more precarious. Since you need to remove the Touch ID cable and transfer it in order to perform to most common repair, replacing a cracked screen, you'd better make damn sure you don't break it. If you do, you'll lose Touch ID functionality and won't be able to get it back.
As for the future of hardware security, who really knows? I've yet to be able to find a reference on another company locking down specific hardware components the way Apple has with Touch ID. It theoretically means they could lock down any component in an iPhone, iPad, iPod, or Mac if they really wanted to. Will they? Probably not. But the option is there.
Your thoughts?
I'm particularly interested to see what you guys think about Touch ID, the tremendous safeguards that have went into building it, and whether or not they truly make you feel comfortable using it. Does this discovery ease your mind at all? Or is it still not enough?
And if there's anyone out there that can cite another example of this kind of hardware lockdown being used, be sure to let us know that too!
Related Topics: denver broncos arcade fire mariano rivera Colorado flooding Allison Micheletti





No comments:
Post a Comment
Note: Only a member of this blog may post a comment.